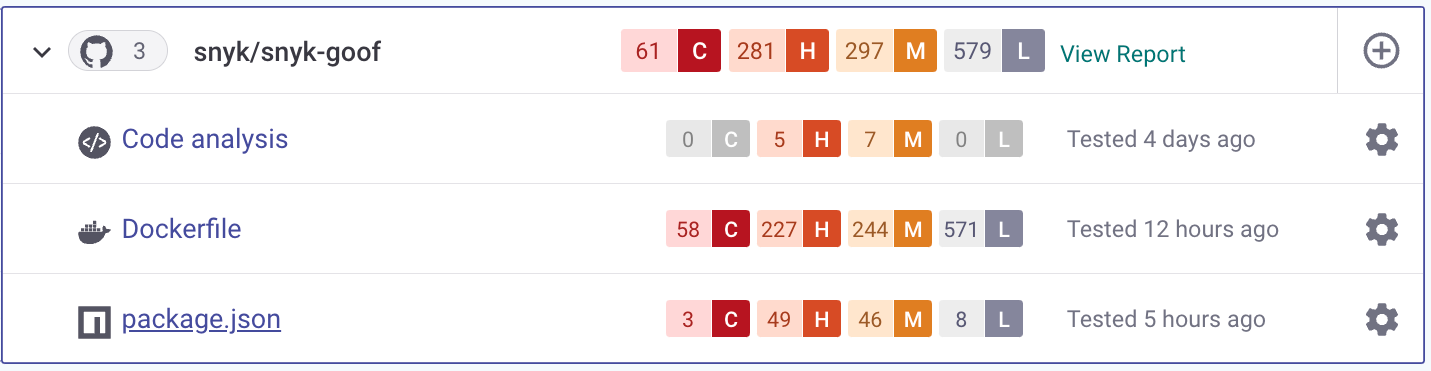
View imported Projects
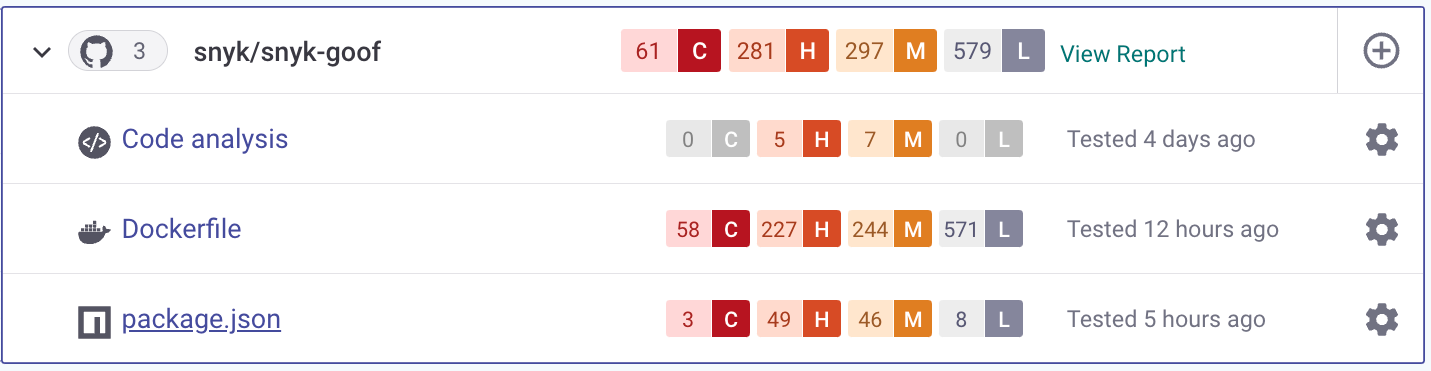
View imported Projects
.png?alt=media)
Vulnerability example - Code analysis
%20(1).png?alt=media)
Vulnerability details Issue Card
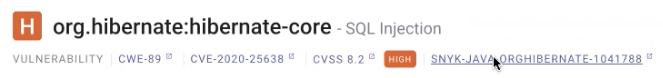
Access Snyk Vulnerability Database
%20(1)%20(1)%20(1)%20(1)%20(1)%20(1)%20(1)%20(1)%20(1)%20(2).png?alt=media)
Snyk Vulnerability Database example entry
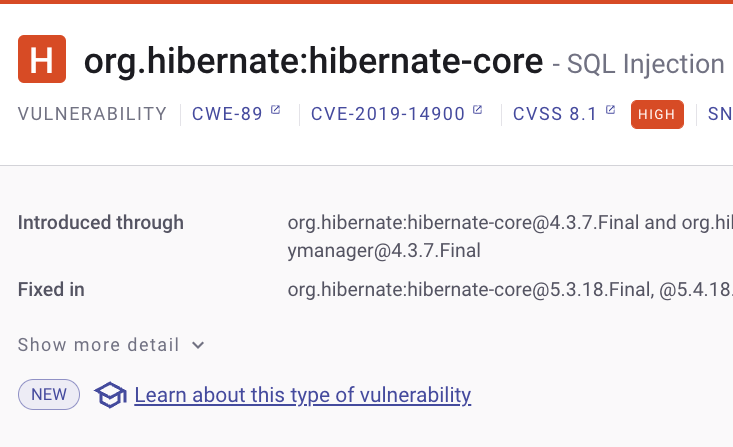
Access Snyk Learn from a vulnerability card

Fix advice for Open Source vulnerabilities
.png?alt=media)
Dependencies for Open Source vulnerabilities
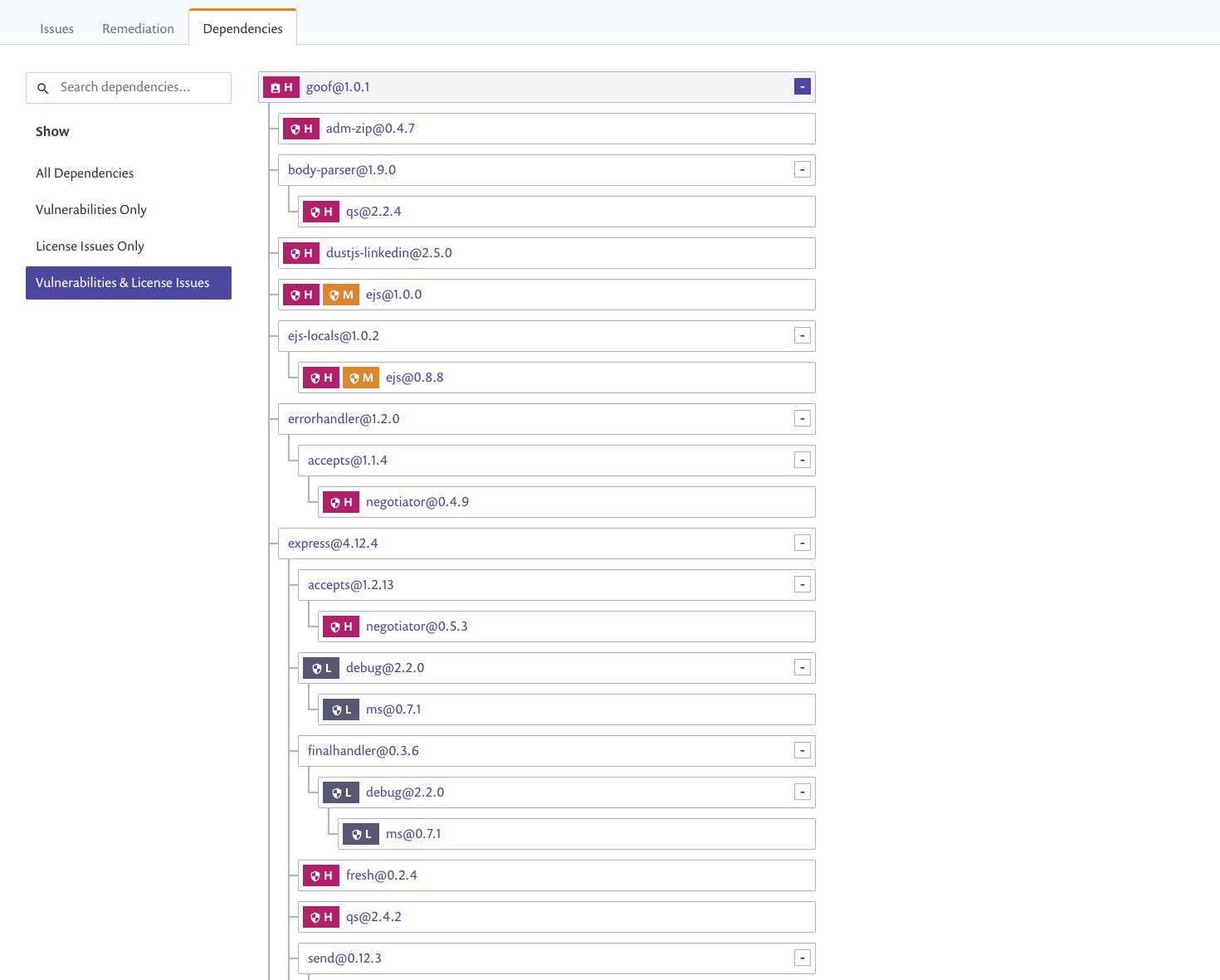
Dependency tree details